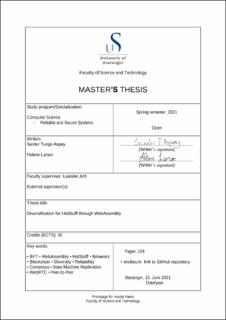
Diversification for HotStuff through WebAssembly
Master thesis
Permanent lenke
https://hdl.handle.net/11250/2786175Utgivelsesdato
2021Metadata
Vis full innførselSamlinger
- Studentoppgaver (TN-IDE) [866]
Sammendrag
By design, the goal of Byzantine Fault Tolerant (BFT) protocols is to protect against malicious or malfunctioning nodes.A BFT protocol in itself is only as secure as the system it is running on.In a perfect world, this would be enough.However, in the real world, multiple layers of security are crucial.Our goal is to expand on the reliability and security provided by existing BFT protocols through diversification with WebAssembly.WasmStuff is a WebAssembly compatible BFT protocol based on relab/hotstuff's [1] implementation of the HotStuff [2] protocol.Consequently, to our knowledge, we have created the first complete browser-based BFT protocol.We looked into different ways of working with WebAssembly, such as using different compilers and running a WebAssembly module inside or outside a browser.Furthermore, we have explored different ways of creating network connections with regards to WebAssembly, and the solution we opted for is described in detail.The networking provided in this thesis is a peer-to-peer connection compatible for use with WebAssembly.Moreover, we designed a runtime for WasmStuff that can be modified to work with other BFT protocols.
Our evaluation shows that WasmStuff performs similarly to relab/hotstuff when it runs on Windows without WebAssembly, which indicates that our modifications for WebAssembly did not impact the performance by much.We met our goal of diversity through the use of WebAssembly as WasmStuff runs in the major browsers.WasmStuff has the ability to run both cross-browser and cross-platform, providing even more diversity.